สามารถติดตามข่าวสารได้ที่ webboard หรือ Facebook NCSA Thailand 
สามารถติดตามข่าวสารได้ที่ webboard หรือ Facebook NCSA Thailand 
สามารถติดตามข่าวสารได้ที่ webboard หรือ Facebook NCSA Thailand 
สามารถติดตามข่าวสารได้ที่ webboard หรือ Facebook NCSA Thailand 
เมื่อวันที่ 9 มิถุนายน 2569 Cybersecurity and Infrastructure Security Agency (CISA) ได้เพิ่มช่องโหว่ใหม่ 7 รายการลงในแคตตาล็อก Known Exploited Vulnerabilities (KEV) จากหลักฐานที่พบว่ามีการโจมตีใช้งานจริงแล้ว มีรายละเอียดดังนี้
ทาง CISA จะปรับปรุงและเพิ่มช่องโหว่ใหม่เข้าสู่แคตตาล็อก KEV อย่างต่อเนื่อง เพื่อให้ครอบคลุมความเสี่ยงที่ตรวจพบจริงในปัจจุบันและอนาคต
สามารถติดตามข่าวสารได้ที่ webboard หรือ Facebook NCSA Thailand 
Industrial Sector
Vulnerabilities
Malware
Breaches/Hacks/Leaks
General News
อ้างอิง
Electronic Transactions Development Agency (ETDA) 
Industrial Sector
New Tooling
Vulnerabilities
Malware
Breaches/Hacks/Leaks
General News
อ้างอิง
Electronic Transactions Development Agency (ETDA) 
New Tooling
Vulnerabilities
Malware
 software, which could allow unauthorized attackers to circumvent security controls and initiate VPN connections. This CVE was added to the Known Exploited Vulnerability (KEV) catalog on May 29."
software, which could allow unauthorized attackers to circumvent security controls and initiate VPN connections. This CVE was added to the Known Exploited Vulnerability (KEV) catalog on May 29."Breaches/Hacks/Leaks
General News
https://www.helpnetsecurity.com/2026/06/05/ai-hallucinations-it-operations-research/
อ้างอิง
Electronic Transactions Development Agency (ETDA) 
สามารถติดตามข่าวสารได้ที่ webboard หรือ Facebook NCSA Thailand 
สามารถติดตามข่าวสารได้ที่ webboard หรือ Facebook NCSA Thailand 
สามารถติดตามข่าวสารได้ที่ webboard หรือ Facebook NCSA Thailand 
สามารถติดตามข่าวสารได้ที่ webboard หรือ Facebook NCSA Thailand 
สามารถติดตามข่าวสารได้ที่ webboard หรือ Facebook NCSA Thailand 
สามารถติดตามข่าวสารได้ที่ webboard หรือ Facebook NCSA Thailand 
ศูนย์ประสานการรักษาความมั่นคงปลอดภัยระบบคอมพิวเตอร์แห่งชาติ (ThaiCERT) ขอแจ้งเตือนการพบช่องโหว่ระดับร้ายแรงในซอฟต์แวร์ Visual Studio Code (VS Code) และสภาพแวดล้อม GitHub.dev ช่องโหว่นี้เปิดโอกาสให้ผู้ไม่หวังดีขโมยสิทธิ์การเข้าถึง (GitHub OAuth Token) ผ่านการหลอกให้เหยื่อเปิดไฟล์หรือลิงก์อันตราย ส่งผลให้ผู้โจมตีสามารถสวมรอยเข้าถึงพื้นที่จัดเก็บซอร์สโค้ด (Repository) ขององค์กร และอาจนำไปสู่การโจมตีห่วงโซ่อุปทาน (Supply Chain Attack) ภัยคุกคามนี้ส่งผลกระทบโดยตรงต่อนักพัฒนา และองค์กรที่มีการเชื่อมต่อบัญชี GitHub เข้ากับระบบดังกล่าว [(1), (2)]
1.รายละเอียดของภัยคุกคาม
ช่องโหว่นี้เกิดจากข้อบกพร่องในการจัดการสิทธิ์ของบัญชีผู้ใช้งานบน GitHub.dev ซึ่งเป็นสภาพแวดล้อมการเขียนโค้ดบนเว็บเบราว์เซอร์ ผู้โจมตีจะอาศัยเทคนิค Social Engineering เพื่อหลอกให้นักพัฒนาเปิดลิงก์ที่สร้างขึ้นมาเป็นพิเศษ หรือเปิดไฟล์สมุดบันทึกโค้ด (Jupyter Notebook) ที่แฝงคำสั่งอันตราย หากการหลอกลวงสำเร็จ ผู้โจมตีจะสามารถดึงข้อมูลโทเคนยืนยันตัวตน (OAuth Token) ของเหยื่อออกไปได้ โทเคนนี้จะเปิดทางให้ผู้โจมตีได้รับสิทธิ์เทียบเท่าเจ้าของบัญชี สามารถเข้าถึงความลับขององค์กร เปลี่ยนแปลงไฟล์ซอร์สโค้ด (Commit/Pull Request) หรือแทรกแซงระบบส่งมอบซอฟต์แวร์อัตโนมัติ (CI/CD Pipelines) ปัจจุบันมีรายงานการเผยแพร่ชุดโค้ดทดสอบการเจาะระบบ (Proof-of-Concept) สู่สาธารณะแล้ว ทำให้มีโอกาสสูงที่จะเกิดการโจมตีจริง [(3), (4)]
2.ผลิตภัณฑ์และผู้ใช้งานที่อาจได้รับผลกระทบ
2.1 ผู้ใช้งาน GitHub.dev ที่เปิด Repository, ไฟล์ Jupyter Notebook หรือลิงก์จากแหล่งที่ไม่น่าเชื่อถือ
2.2 ผู้ใช้งาน Visual Studio Code ที่เชื่อมต่อบัญชี GitHub
2.3 นักพัฒนาโปรแกรมที่ตรวจสอบโค้ดจากบุคคลภายนอก เช่น Pull Request, Repository สาธารณะ หรือไฟล์ที่ได้รับจากภายนอกองค์กร
2.4 หน่วยงานที่มี Repository ส่วนตัวหรือ Repository สำคัญบน GitHub
2.5 องค์กรที่มีการใช้ GitHub ร่วมกับระบบพัฒนาและส่งมอบซอฟต์แวร์ เช่น CI/CD, GitHub Actions หรือระบบจัดการซอร์สโค้ดภายใน
2.6 บัญชีผู้ใช้งานที่มีสิทธิ์สูง เช่น Maintainer, Admin หรือบัญชีที่สามารถแก้ไข Repository สำคัญขององค์กรได้
3.คำแนะนำในการตรวจสอบและป้องกัน
ThaiCERT ขอแนะนำให้ผู้ใช้งาน หน่วยงาน และองค์กรที่มีการใช้งาน Visual Studio Code, GitHub.dev และ GitHub ดำเนินการดังนี้
3.1 หลีกเลี่ยงการเปิดลิงก์ GitHub.dev, ไฟล์ Jupyter Notebook หรือ Repository จากแหล่งที่ไม่น่าเชื่อถือ โดยเฉพาะไฟล์ที่ได้รับจากบุคคลภายนอกหรือแหล่งสาธารณะ
3.2 ตรวจสอบและทบทวนสิทธิ์ของ GitHub OAuth App, GitHub App และ Personal Access Token ที่เชื่อมต่อกับบัญชีผู้ใช้งาน
3.3 ยกเลิก Token หรือแอปพลิเคชันที่ไม่ทราบที่มา ไม่ได้ใช้งานแล้ว หรือมีสิทธิ์เกินความจำเป็น
3.4 ตรวจสอบสิทธิ์การเข้าถึง Repository โดยเฉพาะบัญชีที่มีสิทธิ์อ่านหรือเขียน Repository ส่วนตัวขององค์กร
3.5 จำกัดสิทธิ์ของผู้ใช้งานตามหลัก Least Privilege โดยให้เข้าถึงเฉพาะ Repository และระบบงานที่จำเป็นเท่านั้น
3.6 เปิดใช้งาน Multi-Factor Authentication (MFA) สำหรับบัญชี GitHub ทุกบัญชี โดยเฉพาะบัญชีที่มีสิทธิ์สูง
3.9 พิจารณาใช้นโยบายจำกัดการใช้งาน OAuth App และ GitHub App ในระดับองค์กร เพื่อป้องกันการเชื่อมต่อแอปพลิเคชันที่ไม่ได้รับอนุญาต
3.10 แนะนำให้นักพัฒนาเปิดตรวจสอบโค้ดจากภายนอกในสภาพแวดล้อมแยกต่างหาก เพื่อลดผลกระทบหากไฟล์หรือโค้ดดังกล่าวมีคำสั่งอันตรายแฝงอยู่
4.มาตรการลดความเสี่ยงเร่งด่วน
4.1 ผู้ใช้งานควรออกจากระบบ GitHub.dev และล้าง Cookies หรือ Site Data ของ github.dev ในเว็บเบราว์เซอร์ เพื่อให้ระบบแสดงหน้าต่างยืนยันสิทธิ์ใหม่ก่อนใช้งาน
4.2 หากเคยเปิดลิงก์หรือไฟล์ที่ไม่น่าเชื่อถือผ่าน GitHub.dev ควรตรวจสอบกิจกรรมของบัญชี GitHub โดยทันที
4.3 ผู้ดูแลระบบควรตรวจสอบ Audit Log ของ GitHub Organization เพื่อค้นหากิจกรรมผิดปกติ เช่น การเข้าถึง Repository ที่ไม่สัมพันธ์กับการใช้งานปกติ การสร้าง Token การติดตั้งแอปพลิเคชัน หรือการเปลี่ยนแปลงสิทธิ์
4.4 ตรวจสอบ Repository สำคัญว่ามีการแก้ไขไฟล์ Workflow, Script, Dependency หรือไฟล์กำหนดค่าที่เกี่ยวข้องกับระบบ CI/CD โดยไม่ได้รับอนุญาตหรือไม่
4.5 หากพบพฤติกรรมที่น่าสงสัย ควรยกเลิก Token ที่เกี่ยวข้อง เปลี่ยนรหัสผ่าน ตรวจสอบแอปพลิเคชันที่เชื่อมต่อ และบังคับให้ผู้ใช้งานเข้าสู่ระบบใหม่
4.6 องค์กรควรกำหนดแนวทางให้ผู้ใช้งานหลีกเลี่ยงการเปิดไฟล์ Notebook หรือลิงก์ GitHub.dev จากภายนอก จนกว่าจะตรวจสอบแหล่งที่มาและความน่าเชื่อถือแล้ว
4.7 เพิ่มการเฝ้าระวังเหตุการณ์ผิดปกติที่เกี่ยวข้องกับ GitHub API, GitHub Actions, Repository Permission และการเชื่อมต่อจากตำแหน่งหรืออุปกรณ์ที่ไม่คุ้นเคย
5.แนวทางรับมือเมื่อพบความผิดปกติ
หากหน่วยงานตรวจพบพฤติกรรมผิดปกติที่เกี่ยวข้องกับบัญชี GitHub, GitHub.dev หรือ Repository ขององค์กร เช่น มีการเข้าถึง Repository จากปลายทางที่ไม่คุ้นเคยหรือมีการติดตั้งแอปพลิเคชันที่ไม่ทราบที่มา มี Commit หรือ Pull Request ที่ไม่ได้เกิดจากผู้ใช้งานจริง หรือพบสัญญาณว่า Token อาจถูกนำไปใช้โดยไม่ได้รับอนุญาต ควรดำเนินการดังนี้
5.1 ระงับหรือจำกัดสิทธิ์บัญชีผู้ใช้งานที่เกี่ยวข้องชั่วคราวตามความเหมาะสม
5.2 ยกเลิก GitHub OAuth Token, Personal Access Token และ Session ที่อาจเกี่ยวข้องกับเหตุการณ์
5.3 เปลี่ยนรหัสผ่านบัญชีผู้ใช้งาน และตรวจสอบการเปิดใช้งาน MFA
5.4 ตรวจสอบ OAuth App, GitHub App และส่วนขยายที่เชื่อมต่อกับบัญชีหรือ Organization
5.5 ตรวจสอบ Audit Log, Security Log, GitHub API Log และประวัติการเข้าถึง Repository
5.6 ตรวจสอบ Repository สำคัญว่ามีการเปลี่ยนแปลงไฟล์ โค้ด Workflow หรือค่าการตั้งค่าโดยไม่ได้รับอนุญาตหรือไม่
5.7 ตรวจสอบ Secrets ที่เกี่ยวข้องกับ Repository, GitHub Actions และระบบ CI/CD หากสงสัยว่ามีการรั่วไหลควรดำเนินการ Rotate Secrets โดยทันที
5.8 ตรวจสอบระบบอื่นที่เชื่อมต่อกับ GitHub เช่น ระบบ Build, Deployment, Container Registry, Cloud Platform หรือระบบจัดเก็บ Artifact
5.9 เก็บรักษาหลักฐานที่เกี่ยวข้อง เช่น Audit Log, Commit History, Pull Request, Token Activity และข้อมูลการเชื่อมต่อ เพื่อใช้ในการสืบสวนเหตุการณ์

ด้วยความปรารถนาดี สำนักงานคณะกรรมการการรักษาความมั่นคงปลอดภัยไซเบอร์แห่งชาติ (สกมช.) / ThaiCERT
#ข่าวไซเบอร์ #CyberSecurity #ThaiCERT #GitHub #VSCode #GitHubDev #OAuthToken #SupplyChainAttack #DeveloperSecurity #AppSec #CICD #GitHubSecurity
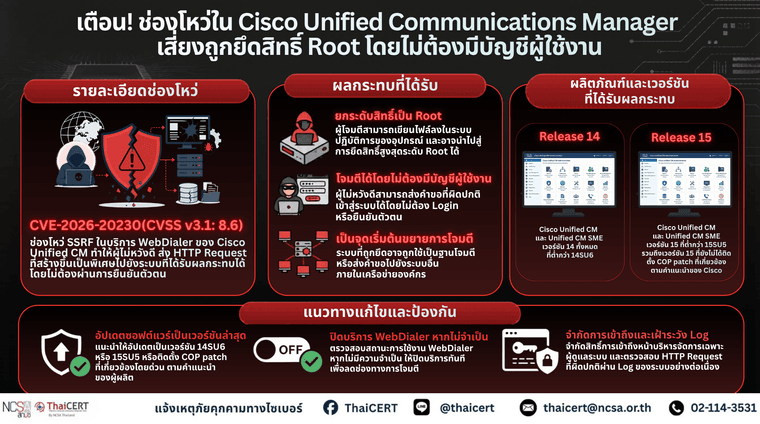
ศูนย์ประสานการรักษาความมั่นคงปลอดภัยระบบคอมพิวเตอร์แห่งชาติ (ThaiCERT) ขอแจ้งเตือนผู้ใช้งาน หน่วยงาน และองค์กรที่มีการใช้งาน Cisco Unified Communications Manager (Unified CM) และ Cisco Unified Communications Manager Session Management Edition (Unified CM SME) ให้เร่งตรวจสอบเวอร์ชันซอฟต์แวร์และสถานะการเปิดใช้งานบริการที่เกี่ยวข้อง
ทั้งนี้ ช่องโหว่นี้มีผลกระทบเฉพาะระบบที่เปิดใช้งานบริการ WebDialer โดยบริการดังกล่าวถูกปิดใช้งานเป็นค่าเริ่มต้น อย่างไรก็ตาม หากหน่วยงานมีการเปิดใช้งานบริการดังกล่าวอยู่ ควรเร่งตรวจสอบและดำเนินการอัปเดตตามคำแนะนำของผู้ผลิตโดยเร็ว เนื่องจากมีรายงานว่ามีโค้ดตัวอย่างสำหรับใช้ทดสอบการโจมตีเผยแพร่ต่อสาธารณะแล้ว แม้ในขณะนี้ยังไม่มีรายงานยืนยันว่าช่องโหว่นี้ถูกนำไปใช้โจมตีจริงในวงกว้าง [1]
1.รายละเอียดช่องโหว่ที่สำคัญ
Cisco Unified Communications Manager เป็นระบบที่ใช้สำหรับบริหารจัดการระบบโทรศัพท์ไอพี การกำหนดเส้นทางการโทร การจัดการอุปกรณ์สื่อสาร และบริการด้านการสื่อสารภายในองค์กร หากระบบดังกล่าวถูกโจมตีสำเร็จ อาจส่งผลกระทบต่อความมั่นคงปลอดภัยของระบบสื่อสารภายในองค์กร รวมถึงอาจถูกใช้เป็นจุดเริ่มต้นในการขยายผลไปยังระบบอื่นที่เชื่อมต่ออยู่ในเครือข่าย โดยรายละเอียดช่องโหว่มีดังนี้
2.ผลกระทบที่อาจเกิดขึ้น
หากหน่วยงานมีการใช้งาน Cisco Unified CM หรือ Cisco Unified CM SME ที่ได้รับผลกระทบ และเปิดใช้งานบริการ WebDialer อาจเกิดผลกระทบดังนี้
2.1 ผู้ไม่หวังดีอาจโจมตีระบบได้ โดยไม่ต้องมีบัญชีผู้ใช้งาน
2.2 อาจทำให้ระบบส่งคำขอไปยังปลายทางภายในหรือปลายทางที่ไม่พึงประสงค์ผ่านช่องโหว่ SSRF
2.3 อาจมีการเขียนไฟล์ลงในระบบปฏิบัติการของอุปกรณ์โดยไม่ได้รับอนุญาต
2.4 อาจถูกนำไปใช้ต่อเพื่อยกระดับสิทธิ์เป็น root
2.5 อาจกระทบต่อระบบโทรศัพท์ไอพี ระบบสื่อสารภายใน และบริการที่พึ่งพา Cisco Unified CM
2.6 อาจถูกใช้เป็นจุดเริ่มต้นในการโจมตีระบบอื่นภายในเครือข่าย
2.7 อาจเพิ่มความเสี่ยงต่อระบบสำคัญขององค์กร หากระบบสื่อสารดังกล่าวเชื่อมต่อกับเครือข่ายภายในหรือระบบบริหารจัดการอื่น
2.8 การมีโค้ดตัวอย่างเผยแพร่สู่สาธารณะอาจเพิ่มโอกาสที่ผู้ไม่หวังดีจะนำช่องโหว่นี้ไปใช้ทดสอบหรือโจมตีระบบที่ยังไม่ได้อัปเดต
3.ผลิตภัณฑ์ที่ได้รับผลกระทบ
3.1 Cisco Unified Communications Manager Release 14 เวอร์ชันก่อนหน้า 14SU6
3.2 Cisco Unified Communications Manager Release 15 เวอร์ชันก่อนหน้า 15SU5 หรือเวอร์ชันที่ยังไม่ได้ติดตั้ง COP patch ที่เกี่ยวข้อง
3.3 Cisco Unified Communications Manager Session Management Edition Release 14 เวอร์ชันก่อนหน้า 14SU6
3.4 Cisco Unified Communications Manager Session Management Edition Release 15 เวอร์ชันก่อนหน้า 15SU5 หรือเวอร์ชันที่ยังไม่ได้ติดตั้ง COP patch ที่เกี่ยวข้อง
4.คำแนะนำในการตรวจสอบและป้องกัน [3][4]
ThaiCERT ขอแนะนำให้ผู้ใช้งาน หน่วยงาน และองค์กรที่มีการใช้งาน Cisco Unified CM หรือ Cisco Unified CM SME ดำเนินการดังนี้
4.1 ตรวจสอบเวอร์ชันซอฟต์แวร์ของระบบ หากเป็นเวอร์ชันที่ได้รับผลกระทบ ควรวางแผนอัปเดตเป็นเวอร์ชันที่ Cisco แนะนำโดยเร็ว
4.2 สำหรับ Cisco Unified CM และ Unified CM SME Release 14 ควรอัปเดตเป็นเวอร์ชัน 14SU6 หรือใหม่กว่า
4.3 สำหรับ Cisco Unified CM และ Unified CM SME Release 15 ควรอัปเดตเป็นเวอร์ชัน 15SU5 เมื่อพร้อมใช้งาน หรือดำเนินการติดตั้ง COP patch ตามคำแนะนำของ Cisco
4.4 ตรวจสอบว่าสภาพแวดล้อมของหน่วยงานมีการเปิดใช้งาน WebDialer service หรือไม่ หากไม่มีความจำเป็นในการใช้งาน ควรพิจารณาปิดใช้งานบริการดังกล่าวเพื่อลดความเสี่ยง
4.5 จำกัดการเข้าถึงหน้าเว็บบริหารจัดการ Cisco Unified CM ให้เข้าถึงได้เฉพาะผู้ดูแลระบบหรือเครือข่ายที่ได้รับอนุญาตเท่านั้น
4.6 ตรวจสอบ firewall, proxy, DNS, SIEM และระบบเฝ้าระวังอื่น ๆ เพื่อค้นหาการเชื่อมต่อหรือ HTTP request ที่ผิดปกติไปยังระบบ Cisco Unified CM
4.7 ตรวจสอบ log ของระบบ Cisco Unified CM โดยเฉพาะช่วงเวลาที่มีการเข้าถึงบริการ WebDialer หรือมีพฤติกรรมการใช้งานที่ผิดปกติ
4.8 หากยังไม่สามารถอัปเดตแพตช์ได้ทันที ควรใช้มาตรการลดความเสี่ยงชั่วคราว เช่น จำกัดการเข้าถึงระบบ ปิดบริการที่ไม่จำเป็น และเพิ่มการเฝ้าระวัง log ที่เกี่ยวข้อง
โดยท่านสามารถติดตามวิธีการแก้ไขจาก Cisco โดยตรงได้ที่ https://dg.th/zmu4g126wq
5.แนวทางรับมือเมื่อพบความผิดปกติ
หากหน่วยงานตรวจพบพฤติกรรมผิดปกติที่เกี่ยวข้องกับ Cisco Unified CM หรือ Cisco Unified CM SME เช่น มีการเข้าถึงบริการ WebDialer จากปลายทางที่ไม่คุ้นเคย มี HTTP request ที่ผิดปกติ มีการเปลี่ยนแปลงไฟล์หรือค่าการตั้งค่าโดยไม่ทราบสาเหตุ หรือพบสัญญาณว่าอาจมีการยกระดับสิทธิ์ ควรดำเนินการดังนี้
5.1 แยกระบบที่เกี่ยวข้องออกจากเครือข่ายหรือจำกัดการเชื่อมต่อชั่วคราวตามความเหมาะสม
5.2 เก็บรักษา log และข้อมูลหลักฐานที่เกี่ยวข้อง เช่น access log, system log, network log และข้อมูลการเปลี่ยนแปลงไฟล์
5.3 ตรวจสอบสถานะของ WebDialer service และบริการอื่นที่เกี่ยวข้อง
5.4 ตรวจสอบบัญชีผู้ดูแลระบบและบัญชีที่มีสิทธิ์สูงว่ามีการใช้งานผิดปกติหรือไม่
5.5 ตรวจสอบว่ามีไฟล์ใหม่ ไฟล์ที่ถูกแก้ไข หรือการเปลี่ยนแปลงค่าระบบที่ไม่สอดคล้องกับการดูแลระบบตามปกติหรือไม่
5.6 ตรวจสอบระบบอื่นในเครือข่ายที่อาจได้รับผลกระทบจากการเชื่อมต่อผ่าน Cisco Unified CM
5.7 ดำเนินการอัปเดตแพตช์หรือใช้มาตรการลดความเสี่ยงตามคำแนะนำของ Cisco
5.8 หากพบหลักฐานการบุกรุกหรือมีความเสี่ยงต่อระบบสำคัญ ควรดำเนินการสืบสวนเหตุการณ์ตามกระบวนการ Incident Response ของหน่วยงาน
ThaiCERT ขอให้หน่วยงานที่มีการใช้งาน Cisco Unified CM และ Cisco Unified CM SME เร่งตรวจสอบทรัพย์สินสารสนเทศของหน่วยงาน ตรวจสอบสถานะการเปิดใช้งาน WebDialer service และดำเนินการอัปเดตซอฟต์แวร์หรือใช้มาตรการลดความเสี่ยงตามคำแนะนำของผู้ผลิตโดยเร็ว โดยเฉพาะหน่วยงานที่ใช้งานระบบดังกล่าวเป็นระบบสื่อสารหลักขององค์กร หรือเชื่อมต่อกับระบบสำคัญภายในเครือข่าย
แหล่งอ้างอิง
[1] https://dg.th/7cwxtfa1i8
[2] https://dg.th/0xagp572uz
[3] https://dg.th/zevdchs39x
[4] https://dg.th/zmu4g126wq
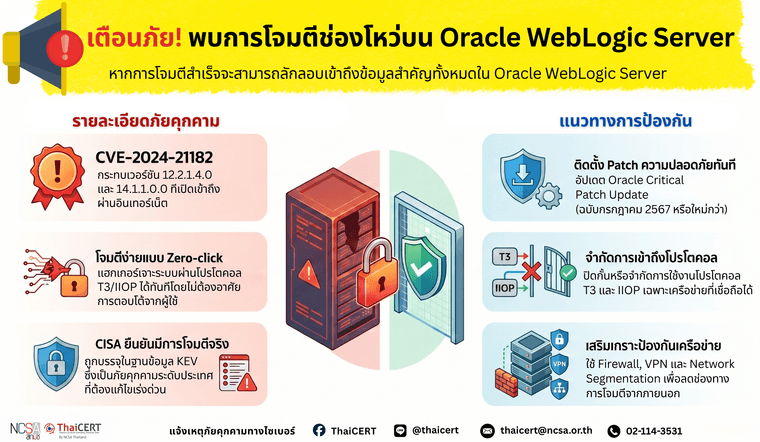
ศูนย์ประสานการรักษาความมั่นคงปลอดภัยระบบคอมพิวเตอร์แห่งชาติ (ThaiCERT) ได้ติดตามสถานการณ์ภัยคุกคามทางไซเบอร์ พบการแจ้งเตือนเกี่ยวช่องโหว่ระดับความรุนแรงสูงในระบบ Oracle WebLogic Server ซึ่งแม้ทางบริษัทผู้พัฒนาจะได้ออก Patch เพื่อแก้ไขช่องโหว่มาตั้งแต่เดือนกรกฎาคม 2567 แล้วก็ตาม แต่ยังพบว่ามีระบบจำนวนมากที่ไม่ได้อัปเดต และยังถูกเปิดให้เข้าถึงได้ผ่านอินเทอร์เน็ต โดยล่าสุด สำนักงานความมั่นคงปลอดภัยไซเบอร์สหรัฐฯ (CISA) ได้ยืนยันว่าช่องโหว่นี้ถูกนำไปใช้โจมตีจริงแล้ว และได้เพิ่มลงในฐานข้อมูลภัยคุกคามระดับประเทศ (KEV) แล้ว [1]
หากการโจมตีสำเร็จ ผู้เจาะระบบจะสามารถลักลอบเข้าถึงข้อมูลสำคัญทั้งหมดที่ Oracle WebLogic Server ดังกล่าวมีสิทธิ์ในการจัดการ [3]
ช่องโหว่นี้สามารถถูกโจมตีผ่านเครือข่าย โดยเฉพาะระบบ Oracle WebLogic Server ที่เปิดให้เข้าถึงบริการผ่านโปรโตคอล T3 หรือ IIOP จากเครือข่ายภายนอก ปัจจุบันยังไม่มีการเปิดเผยรายละเอียดรูปแบบการโจมตี หรือข้อมูลตัวบ่งชี้การโจมตี (Indicators of Compromise: IoCs) สู่สาธารณะ [4]
ผลกระทบ
3.1 ผู้โจมตีที่ไม่ได้ยืนยันตัวตนอาจใช้ช่องโหว่ผ่านเครือข่ายเพื่อ compromise Oracle WebLogic Server
3.2 ผู้โจมตีอาจเข้าถึงข้อมูลสำคัญที่อยู่ภายใต้การเข้าถึงของ Oracle WebLogic Server
3.3 อาจเกิดการรั่วไหลของข้อมูลสำคัญของหน่วยงานหรือข้อมูลที่เกี่ยวข้องกับระบบแอปพลิเคชันภายใน
3.4 ระบบ WebLogic Server ที่เปิดบริการ T3 หรือ IIOP ออกสู่อินเทอร์เน็ต หรืออยู่ในเครือข่ายที่ควบคุมการเข้าถึงไม่รัดกุม มีความเสี่ยงสูงขึ้น
ผลิตภัณฑ์ที่ได้รับผลกระทบ
4.1 Oracle WebLogic Server 12.2.1.4.0
4.2 Oracle WebLogic Server 14.1.1.0.0
4.3 ระบบ Oracle Fusion Middleware ที่ใช้งาน Oracle WebLogic Server เวอร์ชันที่ได้รับผลกระทบ และยังไม่ได้ติดตั้งแพตช์ความปลอดภัยที่เกี่ยวข้อง
แนวทางการแก้ไขและป้องกัน
5.1 ติดตั้งแพตช์ความปลอดภัยจาก Oracle โดยเร็ว โดยอย่างน้อยต้องติดตั้ง Oracle Critical Patch Update ประจำเดือนกรกฎาคม 2567 หรือแพตช์รุ่นใหม่กว่าที่ครอบคลุมการแก้ไข CVE-2024-21182
5.2 ตรวจสอบระบบ Oracle WebLogic Server ภายในหน่วยงานว่ามีการใช้งานเวอร์ชัน 12.2.1.4.0 หรือ 14.1.1.0.0 หรือไม่ และจัดลำดับความสำคัญในการอัปเดตระบบที่เปิดให้เข้าถึงจากภายนอกก่อน
5.3 จำกัดการเข้าถึงโปรโตคอล T3 และ IIOP ให้เฉพาะระบบหรือเครือข่ายที่จำเป็นและเชื่อถือได้เท่านั้น
5.4 หลีกเลี่ยงการเปิด Oracle WebLogic Server หรือพอร์ตบริการที่เกี่ยวข้องกับ WebLogic ให้เข้าถึงจากอินเทอร์เน็ตโดยตรง หากไม่มีความจำเป็น
5.5 ใช้มาตรการควบคุมการเข้าถึงผ่าน firewall, network segmentation, VPN, allowlist และ access control เพื่อลดความเสี่ยงจากการโจมตีผ่านเครือข่าย
5.6 ตรวจสอบ log ของ Oracle WebLogic Server และอุปกรณ์เครือข่ายที่เกี่ยวข้อง เพื่อค้นหาการเชื่อมต่อที่ผิดปกติผ่าน T3/IIOP หรือความพยายามเข้าถึงจากแหล่งที่ไม่น่าเชื่อถือ
5.7 หากไม่สามารถติดตั้งแพตช์หรือดำเนินการลดความเสี่ยงตามคำแนะนำของผู้ผลิตได้ ควรพิจารณาปิดใช้งานระบบหรือแยกระบบออกจากเครือข่ายที่มีความเสี่ยงจนกว่าจะดำเนินการแก้ไขแล้วเสร็จ
ด้วยความปรารถนาดี สำนักงานคณะกรรมการการรักษาความมั่นคงปลอดภัยไซเบอร์แห่งชาติ (สกมช.) / ThaiCERT
#ThaiCERT #CyberSecurity #Alert #NCSA #แจ้งเตือนภัยไซเบอร์ #OracleWebLogic #CVE202421182 #ช่องโหว่ความปลอดภัย #Patchด่วน #ภัยคุกคามไซเบอร์ #DataSecurity #WebLogicServer
#ความมั่นคงปลอดภัยไซเบอร์
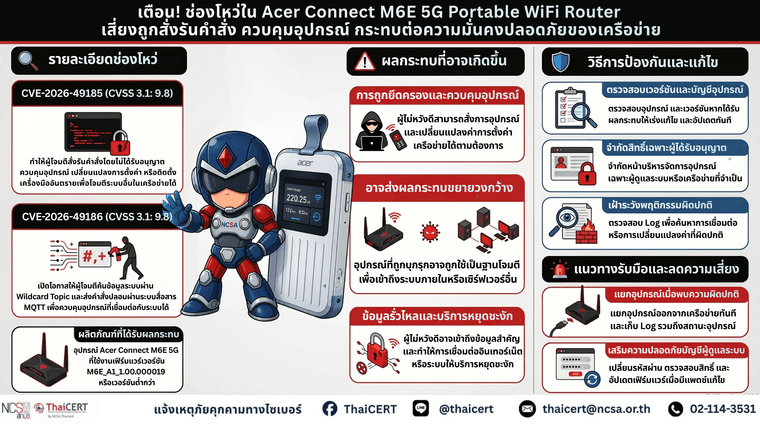
ศูนย์ประสานการรักษาความมั่นคงปลอดภัยระบบคอมพิวเตอร์แห่งชาติ (ThaiCERT) ขอแจ้งเตือนผู้ใช้งาน หน่วยงาน และองค์กรที่มีการใช้งานอุปกรณ์ Acer Connect M6E 5G Portable WiFi Router ให้ตรวจสอบเวอร์ชันเฟิร์มแวร์และติดตามการอัปเดตจากผู้ผลิต เนื่องจากมีรายงานพบช่องโหว่หลายรายการในอุปกรณ์ดังกล่าว ซึ่งเกี่ยวข้องกับการควบคุมการเข้าถึง การตรวจสอบสิทธิ์ การตรวจสอบข้อมูลนำเข้า การป้องกันข้อมูลลับ และกลไกด้านความมั่นคงปลอดภัยของเฟิร์มแวร์ โดยช่องโหว่สำคัญที่ควรเร่งตรวจสอบ ได้แก่ CVE-2026-49185 และ CVE-2026-49186 ซึ่งอาจทำให้ผู้ไม่หวังดีสั่งรันคำสั่งบนอุปกรณ์ แก้ไขค่าการทำงานของระบบ เข้าถึงข้อมูลภายใน หรือใช้เป็นจุดเริ่มต้นในการโจมตีระบบเครือข่ายที่เชื่อมต่ออยู่ได้ [1]
1.รายละเอียดช่องโหว่ที่สำคัญ
1.1 CVE-2026-49185 (CVSS v3.1 เท่ากับ 9.8  ช่องโหว่นี้ถูกจัดอยู่ในประเภท Command Injection หรือการสั่งรันคำสั่งโดยไม่ได้รับอนุญาต หากถูกโจมตีสำเร็จ ผู้ไม่หวังดีอาจสามารถควบคุมอุปกรณ์ เปลี่ยนแปลงการตั้งค่า ติดตั้งเครื่องมือเพิ่มเติม ทำให้อุปกรณ์ทำงานผิดปกติ หรือใช้เป็นจุดเชื่อมต่อเพื่อขยายผลไปยังระบบอื่นในเครือข่ายได้ [2]
ช่องโหว่นี้ถูกจัดอยู่ในประเภท Command Injection หรือการสั่งรันคำสั่งโดยไม่ได้รับอนุญาต หากถูกโจมตีสำเร็จ ผู้ไม่หวังดีอาจสามารถควบคุมอุปกรณ์ เปลี่ยนแปลงการตั้งค่า ติดตั้งเครื่องมือเพิ่มเติม ทำให้อุปกรณ์ทำงานผิดปกติ หรือใช้เป็นจุดเชื่อมต่อเพื่อขยายผลไปยังระบบอื่นในเครือข่ายได้ [2]
1.2 CVE-2026-49186 (CVSS v3.1 เท่ากับ 9.8  Lack of MQTT Broker Topic Access Control Lists ช่องโหว่นี้เกิดจาก MQTT Broker ภายในอุปกรณ์ไม่มีการบังคับใช้รายการควบคุมสิทธิ์ในระดับหัวข้อการสื่อสารอย่างเหมาะสม ทำให้ไคลเอนต์ที่สามารถเข้าถึงบริการดังกล่าวอาจสมัครรับข้อมูลด้วย wildcard เช่น # หรือ + เพื่อสำรวจข้อมูลระบบที่ไม่ควรเข้าถึง หรือส่งคำสั่งปลอมเพื่อควบคุมอุปกรณ์ได้ [3]
Lack of MQTT Broker Topic Access Control Lists ช่องโหว่นี้เกิดจาก MQTT Broker ภายในอุปกรณ์ไม่มีการบังคับใช้รายการควบคุมสิทธิ์ในระดับหัวข้อการสื่อสารอย่างเหมาะสม ทำให้ไคลเอนต์ที่สามารถเข้าถึงบริการดังกล่าวอาจสมัครรับข้อมูลด้วย wildcard เช่น # หรือ + เพื่อสำรวจข้อมูลระบบที่ไม่ควรเข้าถึง หรือส่งคำสั่งปลอมเพื่อควบคุมอุปกรณ์ได้ [3]
2.ผลกระทบที่อาจเกิดขึ้น
หากหน่วยงานมีการใช้งานอุปกรณ์ Acer Connect M6E 5G Portable WiFi Router ที่ได้รับผลกระทบ และยังไม่ได้ดำเนินการควบคุมความเสี่ยง อาจเกิดผลกระทบดังนี้
2.1 ผู้ไม่หวังดีอาจสามารถสั่งรันคำสั่งบนอุปกรณ์ได้โดยไม่ได้รับอนุญาต
2.2 อาจมีการเปลี่ยนแปลงค่าการตั้งค่าเครือข่ายหรือค่าการทำงานของอุปกรณ์
2.3 อาจมีการเข้าถึงข้อมูลของอุปกรณ์หรือข้อมูลที่เกี่ยวข้องกับเครือข่าย
2.4 อุปกรณ์อาจถูกใช้เป็นจุดเริ่มต้นในการโจมตีระบบอื่นภายในเครือข่าย
2.5 อาจเกิดการหยุดชะงักของบริการ การเชื่อมต่ออินเทอร์เน็ต หรือบริการเครือข่ายที่พึ่งพาอุปกรณ์ดังกล่าว
2.6 อาจมีการนำอุปกรณ์ไปใช้เป็นช่องทางสื่อสาร ควบคุม หรือสนับสนุนการโจมตีในระยะถัดไป
2.7 ในกรณีที่อุปกรณ์เชื่อมต่อกับระบบสำคัญ อาจเพิ่มความเสี่ยงต่อระบบงานภายใน ระบบให้บริการประชาชน หรือระบบที่มีข้อมูลสำคัญของหน่วยงาน
นอกจาก CVE-2026-49185 และ CVE-2026-49186 แล้ว รายงานจากผู้ผลิตยังระบุช่องโหว่อื่นที่เกี่ยวข้องกับการใช้ข้อมูลลับแบบฝังในระบบ การกำหนดสิทธิ์ไม่เหมาะสม การเปิดเผยข้อมูลผ่านระบบจัดเก็บข้อมูล การข้ามการยืนยันตัวตน การจัดการ eSIM โดยไม่มีการตรวจสอบสิทธิ์ การตรวจสอบใบรับรอง TLS ไม่เหมาะสม และการคงอยู่ของส่วนทดสอบหรือส่วนวินิจฉัยในเฟิร์มแวร์ ซึ่งสะท้อนว่าความเสี่ยงไม่ได้จำกัดอยู่เพียงช่องโหว่รายการใดรายการหนึ่ง แต่เป็นความเสี่ยงโดยรวมของอุปกรณ์และเฟิร์มแวร์ที่ใช้งานอยู่
3 ผลิตภัณฑ์ที่ได้รับผลกระทบ
4.คำแนะนำในการตรวจสอบและป้องกัน
ThaiCERT ขอแนะนำให้ผู้ใช้งาน หน่วยงาน และองค์กรที่มีการใช้งานอุปกรณ์ Acer Connect M6E 5G Portable WiFi Router ดำเนินการดังนี้
4.1 จัดทำรายการอุปกรณ์เครือข่ายที่ใช้งานจริงในหน่วยงาน พร้อมระบุรุ่น เวอร์ชันเฟิร์มแวร์ ผู้รับผิดชอบ และสถานะการอัปเดต เพื่อให้สามารถติดตามความเสี่ยงและดำเนินการแก้ไขได้อย่างรวดเร็ว
4.2 ตรวจสอบเวอร์ชันเฟิร์มแวร์ของอุปกรณ์ หากเป็นเวอร์ชัน M6E_AI_1.00.000019 หรือก่อนหน้า ให้ถือว่าอยู่ในกลุ่มที่ได้รับผลกระทบ
4.3 จำกัดการเข้าถึงหน้าเว็บบริหารจัดการอุปกรณ์ ให้เข้าถึงได้เฉพาะผู้ดูแลระบบหรือเครือข่ายที่จำเป็นเท่านั้น
4.4 ตรวจสอบ log ของ firewall, proxy, DNS, endpoint, SIEM หรือระบบเฝ้าระวังอื่น ๆ เพื่อค้นหาพฤติกรรมผิดปกติ เช่น การเชื่อมต่อไปยังปลายทางที่ไม่คุ้นเคย การเปลี่ยนแปลงค่าการตั้งค่า หรือการใช้งานระบบบริหารจัดการนอกเวลาทำการ
4.5 หลีกเลี่ยงการนำอุปกรณ์ที่ยังไม่ได้อัปเดตเฟิร์มแวร์ไปใช้งานร่วมกับระบบสำคัญหรือเครือข่ายที่มีข้อมูลอ่อนไหว
5.แนวทางรับมือเมื่อพบความผิดปกติ
หากหน่วยงานตรวจพบว่าอุปกรณ์ Acer Connect M6E 5G Portable WiFi Router มีพฤติกรรมผิดปกติ เช่น มีการเปลี่ยนแปลงค่าการตั้งค่าโดยไม่ทราบสาเหตุ มีการเชื่อมต่อไปยังปลายทางภายนอกที่ไม่รู้จัก มีการรีสตาร์ทหรือทำงานผิดปกติ หรือพบสัญญาณว่าอาจมีการเข้าถึงระบบบริหารจัดการโดยไม่ได้รับอนุญาต ควรดำเนินการดังนี้
5.1 แยกอุปกรณ์ออกจากเครือข่ายชั่วคราวเพื่อลดความเสี่ยง
5.2 บันทึกข้อมูลสถานะของอุปกรณ์ เช่น เวอร์ชันเฟิร์มแวร์ การตั้งค่าเครือข่าย log และเวลาที่พบเหตุการณ์
5.3 เปลี่ยนรหัสผ่านบัญชีผู้ดูแลระบบและบัญชีที่เกี่ยวข้อง
5.4 ดำเนินการอัปเดตเฟิร์มแวร์เมื่อมีแพตช์จากผู้ผลิต และตรวจสอบการตั้งค่าหลังอัปเดต
5.5 หากพบหลักฐานการบุกรุกหรือมีความเสี่ยงต่อระบบสำคัญ ควรดำเนินการสืบสวนเหตุการณ์ตามกระบวนการ Incident Response ของหน่วยงาน
ThaiCERT ขอให้หน่วยงานที่มีการใช้งานอุปกรณ์รุ่นดังกล่าวเร่งตรวจสอบทรัพย์สินสารสนเทศของหน่วยงาน ประเมินความเสี่ยงตามบริบทการใช้งานจริง และดำเนินมาตรการลดความเสี่ยงชั่วคราวระหว่างรอเฟิร์มแวร์แก้ไขจากผู้ผลิต โดยเฉพาะกรณีที่อุปกรณ์ถูกใช้งานร่วมกับระบบสำคัญ ระบบเครือข่ายภายใน หรือระบบที่เกี่ยวข้องกับการให้บริการประชาชน
ด้วยความปรารถนาดี สำนักงานคณะกรรมการการรักษาความมั่นคงปลอดภัยไซเบอร์แห่งชาติ (สกมช.) / ThaiCERT
#ThaiCERT #CyberSecurity #Alert #NCSA #แจ้งเตือนภัยไซเบอร์ #ช่องโหว่ร้ายแรง #AcerConnectM6E #CVE202649185 #CVE202649186 #WiFiRouter #อัปเดตเฟิร์มแวร์
#ความมั่นคงปลอดภัยไซเบอร์
สามารถติดตามข่าวสารได้ที่ webboard หรือ Facebook NCSA Thailand 
สามารถติดตามข่าวสารได้ที่ webboard หรือ Facebook NCSA Thailand 
สามารถติดตามข่าวสารได้ที่ webboard หรือ Facebook NCSA Thailand 